| [1] |
LU Yiqin, HUANG Chenghai, CHEN Jiarui, et al.
Time Sensitive Network Scheduling Method Based on Genetic Algorithm
[J]. Journal of South China University of Technology(Natural Science Edition), 2024, 52(2): 1-12.
|
| [2] |
LIU Ning, HUA Tianbiao, WANG Gao, et al.
A Batch Scheduling Method of Flexible Job-Shop with Partially Out-of-Ordered Execute Operation
[J]. Journal of South China University of Technology(Natural Science Edition), 2024, 52(10): 51-63.
|
| [3] |
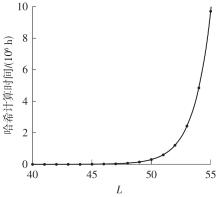
QIN Jiancheng, ZHONG Yu, CHENG Zhe, et al.
Fast Modulus Algorithm for Internet of Things Key Exchange Based on Mersenne-like Numbers
[J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(5): 24-35.
|
| [4] |
LU Qingchang, XU Biao, CUI Xin .
Research on the Non-linear Relationship Between Built Environment and Bike-sharing Flow Rate
[J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(2): 100-110.
|
| [5] |
LU Yiqin, XIONG Xin, WANG Meng, et al..
A Bandwidth Allocation Method of AVB Traffic Based on Link Load Balancing in TSN
[J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(11): 1-9.
|
| [6] |
BIE Yiming, ZHU Aoze, CONG Yuan.
Electric Bus Scheduling Method Considering Differences in the State of Health of Batteries
[J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(10): 11-21.
|
| [7] |
YANG Min, CHEN Shantao, JIANG Ruiyu, et al.
Flexible Bus Scheduling Optimization for Integrated Hub Connections in the Context of MaaS
[J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(10): 22-30.
|
| [8] |
WENG Jiancheng, WANG Maolin, LIN Pengfei, et al.
Cross-line Combined Bus Scheduling Optimization Method Based on Passenger Flow Characteristic Identification
[J]. Journal of South China University of Technology(Natural Science Edition), 2022, 50(9): 39-48.
|
| [9] |
XIA Qinxiang, LI Kai, MA Jun, et al.
Die Electrode Scheduling Problem Solution Based on Genetic Algorithm
[J]. Journal of South China University of Technology(Natural Science Edition), 2022, 50(3): 80-87.
|
| [10] |
WU Haowei, HUANG Fengjiao, YAN Lian, et al.
Legitimate Eavesdropping Scheme for Suspicious Relay Communication Networks
[J]. Journal of South China University of Technology(Natural Science Edition), 2022, 50(10): 70-79.
|
| [11] |
TAN Guang LI Changhao ZHAN Zhaohuan.
Adaptive Scheduling Algorithm for Object Detection and
Tracking Based on Device-Cloud Collaboration
[J]. Journal of South China University of Technology (Natural Science Edition), 2021, 49(7): 86-93.
|
| [12] |
QUAN Yanming HE Yiming.
Research on Clonal Selection Algorithm for Multi-Robot Task Allocation and Scheduling
[J]. Journal of South China University of Technology (Natural Science Edition), 2021, 49(5): 102-110.
|
| [13] |
HAN Wanli, DU Bangshen, ZHAO Jianyou, et al.
Optimization of Urban and Rural Public Transport Operation and Scheduling Considering Small Piece Express
[J]. Journal of South China University of Technology (Natural Science Edition), 2021, 49(5): 28-37.
|
| [14] |
JIN Wenzhou, HU Weiyang, DENG Jiayi, et al.
Flexible Scheduling Model of Demand Response Transit
Based on Hybrid Algorithm
[J]. Journal of South China University of Technology (Natural Science Edition), 2021, 49(1): 123-133.
|
| [15] |
LIN Shunjiang, TANG Zhiqiang, XIE Yuquan, et al.
Distributed Calculation of Security-Constrained Optimal Energy Flow in Integrated Power and Gas Energy Systems
[J]. Journal of South China University of Technology (Natural Science Edition), 2020, 48(7): 36-46.
|