Journal of South China University of Technology(Natural Science Edition) ›› 2024, Vol. 52 ›› Issue (6): 110-119.doi: 10.12141/j.issn.1000-565X.230105
• Computer Science & Technology • Previous Articles Next Articles
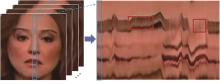
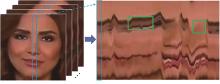
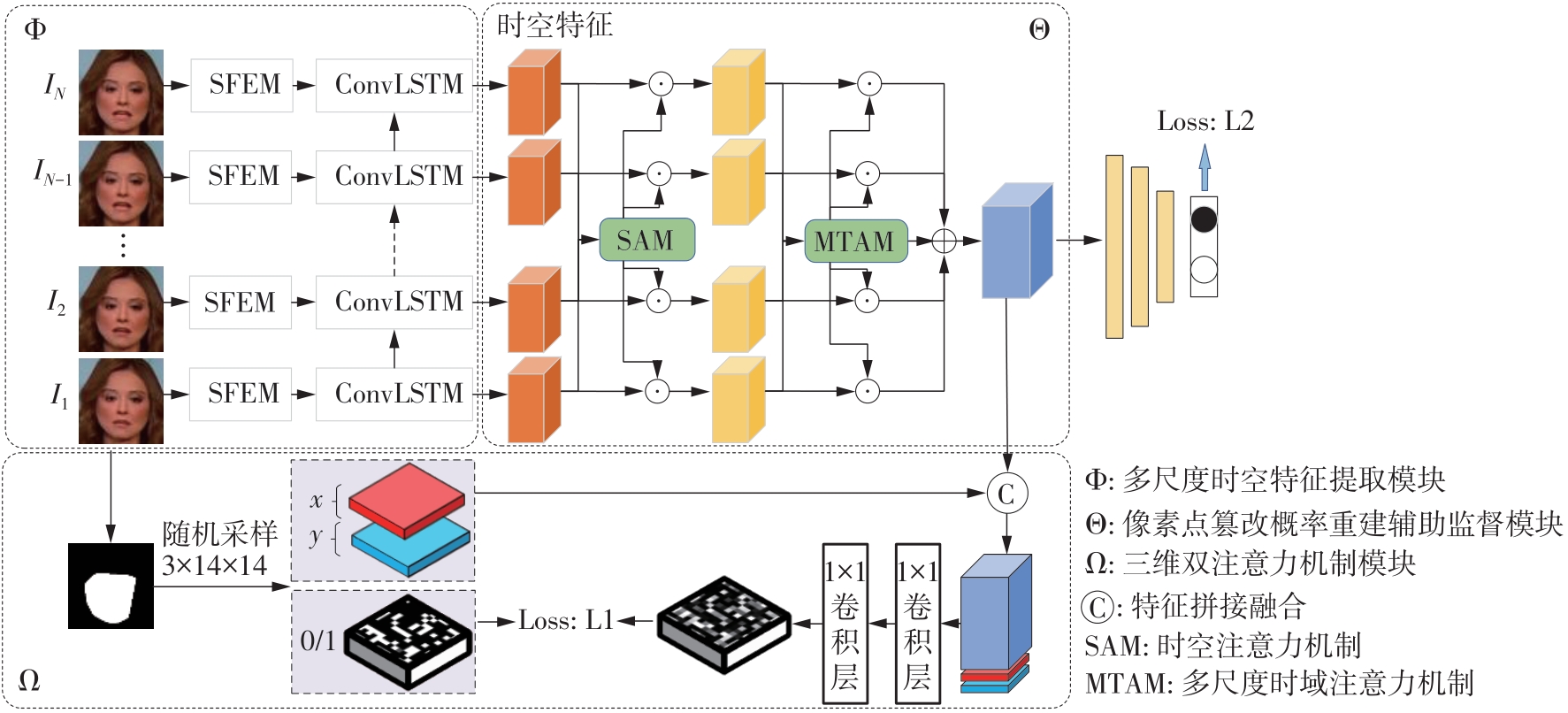
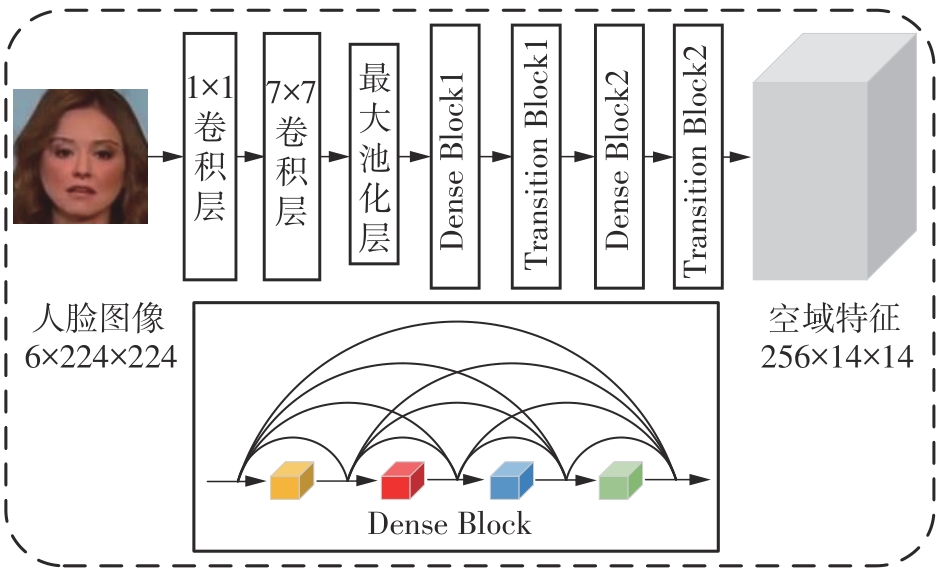
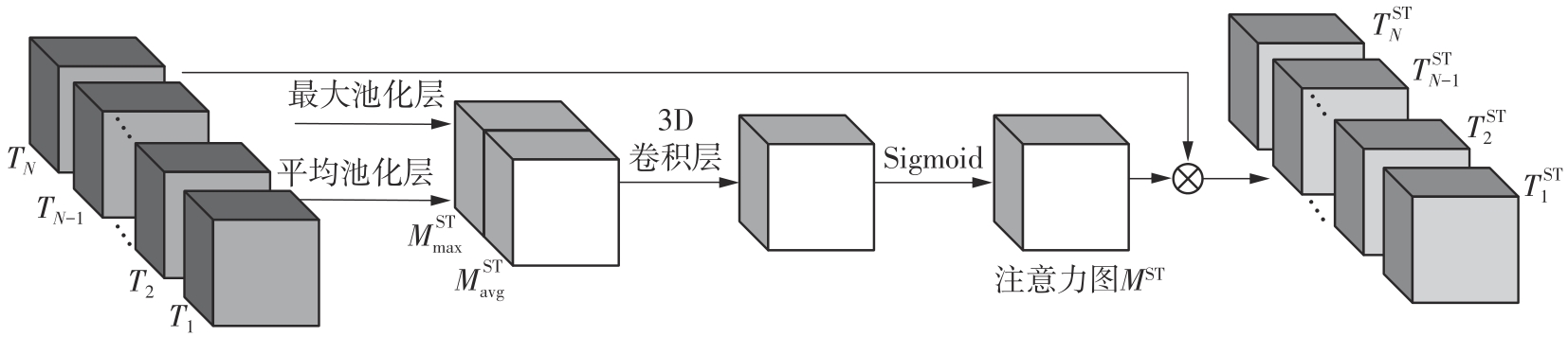
Improvement of Cross-Dataset Performance of Face Forgery Detection Based on Multi-Scale Spatiotemporal Features and Tampering Probabilities
HU Yongjian1( ), ZHUO Sichao1, LIU Beibei1(
), ZHUO Sichao1, LIU Beibei1( ), WANG Yufei2, LI Jicheng1
), WANG Yufei2, LI Jicheng1
- 1.School of Electronic and Information Engineering,South China University of Technology,Guangzhou 510640,Guangdong,China
2.School of Criminal Science and Technology,Guangdong Police College,Guangzhou 510440,Guangdong,China
-
Received:2023-03-13Online:2024-06-25Published:2023-11-08 -
Contact:刘琲贝(1980—),女,讲师,硕士生导师,主要从事多媒体信息安全研究。 E-mail:eebbliu@scut.edu.cn -
About author:胡永健(1962—),男,教授,博士生导师,主要从事多媒体信息安全、图像处理、人工智能及其应用等研究。E-mail: eeyjhu@scut.edu.cn -
Supported by:the Scientific Research Capability Improvement Program for Key Discipline Construction of Guangdong Province(2021ZDJS047);the Characteristic Innovation Project of Colleges and Universities in Guangdong Province (Natural Science)(2023KTSCX093)
CLC Number:
Cite this article
HU Yongjian, ZHUO Sichao, LIU Beibei, WANG Yufei, LI Jicheng. Improvement of Cross-Dataset Performance of Face Forgery Detection Based on Multi-Scale Spatiotemporal Features and Tampering Probabilities[J]. Journal of South China University of Technology(Natural Science Edition), 2024, 52(6): 110-119.
share this article
Table 2
Cross-dataset test results from FF++ to other databases"
| 检测算法 | 不同数据库上的AUC/% | 平均AUC/% | ||
|---|---|---|---|---|
| DFD | DFDC | CDF | ||
| Xception[ | 83.16 | 67.90 | 59.46 | 70.17 |
| Face X-ray[ | 85.60 | 70.01 | 74.20 | 76.94 |
| SPSL[ | 83.23 | 75.56 | 76.88 | 78.56 |
| Two-Stream HF[ | 91.90 | 79.70 | 79.40 | 83.73 |
| LRL-Net[ | 89.24 | 76.53 | 78.26 | 81.34 |
| CORE[ | 93.74 | 75.74 | 79.45 | 82.98 |
| 3D R50-FTCN[ | 90.52 | 79.97 | 79.85 | 83.45 |
| DCL[ | 91.66 | 76.71 | 82.30 | 83.56 |
| 文中算法 | 95.37 | 85.31 | 81.43 | 87.37 |
Table 3
Test results among different forgery methods"
| 伪造方法 | 检测算法 | 不同伪造方法下的AUC/% | 平均AUC/% | |||
|---|---|---|---|---|---|---|
| DF | F2F | FS | NT | |||
| DF | Xception[ | 99.32 | 73.60 | 49.05 | 73.61 | 73.90 |
| Face X-ray[ | 98.71 | 63.31 | 60.06 | 69.82 | 72.98 | |
| Two-Stream HF[ | 99.21 | 76.43 | 49.75 | 81.42 | 76.70 | |
| DCL[ | 99.98 | 77.13 | 61.01 | 75.01 | 78.28 | |
| 文中算法 | 99.95 | 77.66 | 53.25 | 84.14 | 78.75 | |
| F2F | Xception[ | 80.33 | 99.47 | 76.25 | 69.66 | 81.50 |
| Face X-ray[ | 45.82 | 98.15 | 96.12 | 94.57 | 87.47 | |
| Two-Stream HF[ | 83.71 | 99.45 | 98.77 | 98.46 | 95.10 | |
| DCL[ | 91.91 | 99.21 | 59.58 | 66.67 | 79.34 | |
| 文中算法 | 88.25 | 99.89 | 85.29 | 81.24 | 88.67 | |
| FS | Xception[ | 66.45 | 88.83 | 99.40 | 71.32 | 81.43 |
| Face X-ray[ | 63.02 | 98.44 | 93.83 | 94.57 | 83.96 | |
| Two-Stream HF[ | 68.80 | 99.38 | 99.54 | 98.01 | 91.43 | |
| DCL[ | 74.80 | 69.75 | 99.90 | 52.60 | 74.26 | |
| 文中算法 | 57.28 | 89.46 | 99.82 | 71.61 | 79.54 | |
| NT | Xception[ | 79.98 | 81.36 | 73.17 | 99.15 | 83.42 |
| Face X-ray[ | 70.51 | 91.77 | 91.03 | 92.54 | 86.46 | |
| Two-Stream HF[ | 89.40 | 99.52 | 93.35 | 99.46 | 96.93 | |
| DCL[ | 91.23 | 52.13 | 79.31 | 98.97 | 80.41 | |
| 文中算法 | 93.81 | 94.08 | 94.77 | 99.91 | 93.14 | |
Table 4
Intra-dataset test results under different video quality"
| 检测算法 | ACC/% | AUC/% | ||
|---|---|---|---|---|
| FF++(c23) | FF++(c40) | FF++(c23) | FF++(c40) | |
| Xception[ | 95.73 | 86.86 | 96.30 | 89.30 |
| Face X-ray[ | — | — | 87.40 | 61.60 |
| SPSL[ | 91.50 | 81.57 | 95.32 | 82.82 |
| Two-Stream HF[ | 97.74 | 88.95 | 99.36 | 94.10 |
| LRL-Net[ | 97.59 | 91.47 | 99.46 | 95.21 |
| CORE[ | 97.61 | 87.99 | 99.66 | 90.61 |
| 3D R50-FTCN[ | 96.65 | 90.72 | 99.23 | 94.78 |
| DCL[ | 93.58 | 89.95 | 99.30 | 94.94 |
| 文中算法 | 97.76 | 91.48 | 99.70 | 95.56 |
| 1 | LI Y,LYU S .Exposing DeepFake videos by detecting face warping artifacts[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition.Long Beach:IEEE,2019:46-52. |
| 2 | LI J, XIE H, LI J,et al .Frequency-aware discriminative feature learning supervised by single-center loss for face forgery detection[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition.Virtual:IEEE,2021:6458-6467. |
| 3 | DURALL R, KEUPER M, KEUPER J .Watch your up-convolution:CNN-based generative deep neural networks are failing to reproduce spectral distributions[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern recognition.Seattle:IEEE,2020:7890-7899. |
| 4 | LI L, BAO J, ZHANG T,et al .Face X-ray for more general face forgery detection[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition.Seattle:IEEE,2020:5001-5010. |
| 5 | 胡永健,高逸飞,刘琲贝,等 .基于图像分割网络的深度假脸视频篡改检测[J].电子与信息学报,2021,43(1):162-170. |
| HU Yongjian, GAO Yifei, LIU Beibei,et al .Deepfake videos detection based on image segmentation with deep neural networks[J].Journal of Electronics & Information Technology,2021,43(1):162-170. | |
| 6 | YANG X, LI Y,LYU S .Exposing deep fakes using inconsistent head poses[C]∥Proceedings of the 2019 IEEE International Conference on Acoustics,Speech and Signal Processing.Bredo:IEEE,2019:8261-8265. |
| 7 | HALIASSOS A, VOUGIOUKAS K, PETRIDIS S,et al .Lips don’t lie:a generalisable and robust approach to face forgery detection[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition.Virtual:IEEE,2021:5039-5049. |
| 8 | AMERINI I, CALDELLI R .Exploiting prediction error inconsistencies through LSTM-based classifiers to detect deepfake videos[C]∥Proceedings of the 2020 ACM Workshop on Information Hiding and Multimedia Security.Denver:ACM,2020:97-102. |
| 9 | MASI I, KILLEKAR A, MASCARENHAS R,et al .Two-branch recurrent network for isolating deepfakes in videos[C]∥Proceedings of the 16th European Confe-rence on Computer Vision.Glasgow:Springer,2020:23-28. |
| 10 | ZHENG Y, BAO J, CHEN D,et al .Exploring temporal coherence for more general video face forgery detection[C]∥Proceedings of the IEEE/CVF International Conference on Computer Vision and Pattern Recognition.Virtual:IEEE,2021:15044-15054. |
| 11 | LI X, WAN J, JIN Y,et al .3DPC-Net:3D point cloud network for face anti-spoofing[C]∥Proceedings of the 2020 IEEE International Joint Conference on Biometrics.Houston:IEEE,2020:1-8. |
| 12 | SHI X, CHEN Z, WANG H,et al .Convolutional LSTM network:a machine learning approach for precipitation nowcasting[J].Advances in Neural Information Processing Systems,2015,28:802-810. |
| 13 | ROSSLER A, COZZOLINO D, VERDOLIVA L,et al .Faceforensics++:learning to detect manipulated facial images[C]∥Proceedings of the IEEE/CVF International Conference on Computer Vision and Pattern Recognition.Long Beach:IEEE,2019:1-11. |
| 14 | LIU H, LI X, ZHOU W,et al .Spatial-phase shallow learning:rethinking face forgery detection in frequency domain[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition.Virtual:IEEE,2021:772-781. |
| 15 | LUO Y, ZHANG Y, YAN J,et al .Generalizing face forgery detection with high-frequency features[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition.Virtual:IEEE,2021:16317-16326. |
| 16 | CHEN S, YAO T, CHEN Y,et al .Local relation learning for face forgery detection[C]∥Proceedings of the AAAI Conference on Artificial Intelligence.Virtual:AAAI,2021,35(2):1081-1088. |
| 17 | NI Y, MENG D, YU C,et al .CORE:consistent representation learning for face forgery detection[C]∥Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition.New Orleans:IEEE,2022:12-21. |
| 18 | SUN K, YAO T, CHEN S,et al .Dual contrastive learning for general face forgery detection[C]∥Proceedings of the AAAI Conference on Artificial Intelligence.Virtual:AAAI,2022:2316-2324. |
| [1] | ZHOU Lang, FAN Kun, QU Hua, et al. Forest Fire Recognition by Improved EfficientNet-E Model Based on ECA Attention Mechanism [J]. Journal of South China University of Technology(Natural Science Edition), 2024, 52(2): 42-49. |
| [2] | TIAN Sheng, SONG Lin, ZHAO Kailong. Point Cloud Classification Based on Offset Attention Mechanism and Multi-Feature Fusion [J]. Journal of South China University of Technology(Natural Science Edition), 2024, 52(1): 100-109. |
| [3] | LI Jiachun, LI Bowen, LIN Weiwei. AdfNet: An Adaptive Deep Forgery Detection Network Based on Diverse Features [J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(9): 82-89. |
| [4] | LI Haiyan, YIN Haolin, LI Peng, et al.. Image Inpainting Algorithm Based on Dense Feature Reasoning and Mix Loss Function [J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(9): 99-109. |
| [5] | GUO Enqiang, FU Xinsha. Dropped Object Detection Method Based on Feature Similarity Learning [J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(6): 30-41. |
| [6] | LIU Yupeng, ZHANG Lei. Cognitive Diagnosis Model Integrating Forgetting and Importance of Knowledge Points [J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(5): 54-62. |
| [7] | LU Lu, LAI Jinxiong. Smart Contract Vulnerability Detection Method Based on Capsule Network and Attention Mechanism [J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(5): 36-44. |
| [8] | ZHAO Rongchao, WU Baili, CHEN Zhuyun, et al. Graph Neural Network for Fault Diagnosis with Multi-Scale Time-Spatial Information Fusion Mechanism [J]. Journal of South China University of Technology(Natural Science Edition), 2023, 51(12): 42-52. |
| [9] | WO Yan, LIANG Jiyun, HAN Guoqiang. A cross-modal face retrieval method based on metric learning [J]. Journal of South China University of Technology(Natural Science Edition), 2022, 50(6): 1-9. |
| [10] | HUANG Min QI Haitao JIANG Chunlin. Coupled Collaborative Filtering Model Based on Attention Mechanism [J]. Journal of South China University of Technology(Natural Science Edition), 2021, 49(7): 59-65. |
| [11] | LIU Huiting, LI Yinjie, GUO Lingling, et al. Tightly Coupled Recommendation Algorithm Based on Heterogeneous Information Networks [J]. Journal of South China University of Technology (Natural Science Edition), 2021, 49(7): 66-75. |
| [12] | IKA Novita Dewi, CAI Xiaoling, et al. Drug-Drug Interaction Extraction Model Combining Category Keywords with Attention Mechanism [J]. Journal of South China University of Technology (Natural Science Edition), 2021, 49(1): 10-17. |
| [13] | LIU Huiting, JI Qiang, LIU Huimin, et al. Joint Deep Recommendation Model Based on Double-Layer Attention Mechanism [J]. Journal of South China University of Technology (Natural Science Edition), 2020, 48(6): 97-105. |
| Viewed | ||||||
|
Full text |
|
|||||
|
Abstract |
|
|||||