

收稿日期: 2022-06-06
网络出版日期: 2023-01-16
基金资助
广东省重点领域研发计划项目(2020B0101120002);广东省科技厅海外名师项目(科技类)(粤财科教[2021]157号)
Fast Modulus Algorithm for Internet of Things Key Exchange Based on Mersenne-like Numbers
Received date: 2022-06-06
Online published: 2023-01-16
Supported by
the Key-Area R&D Program of Guangdong Province(2020B0101120002)
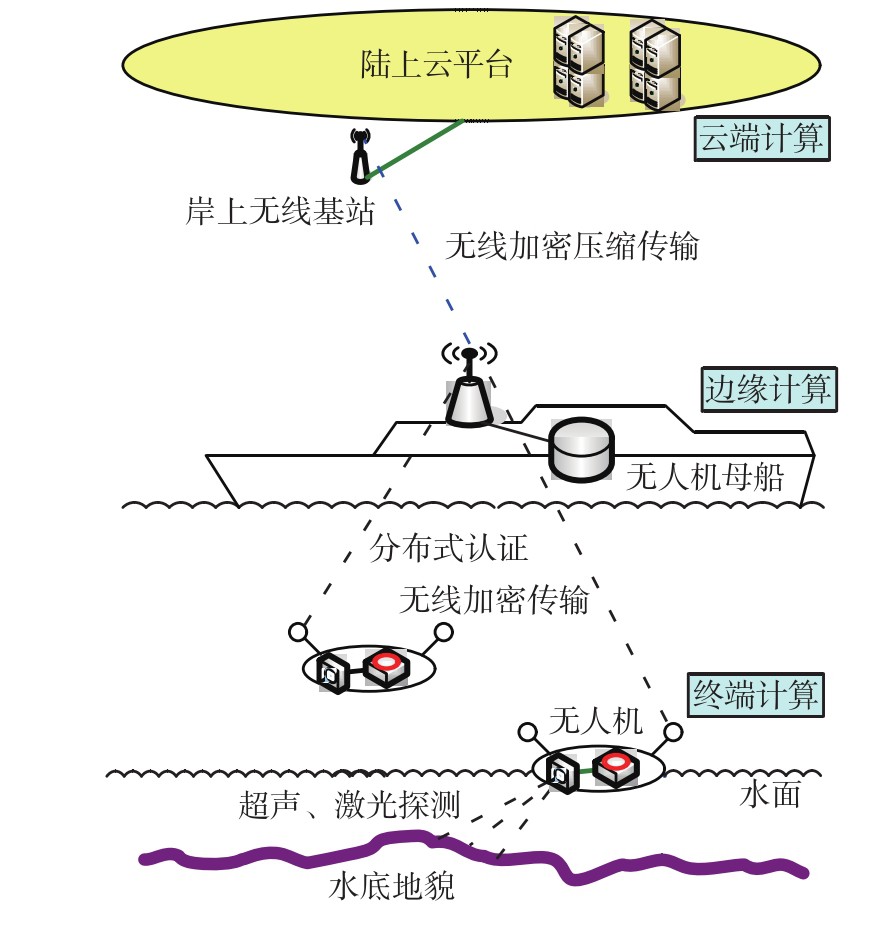
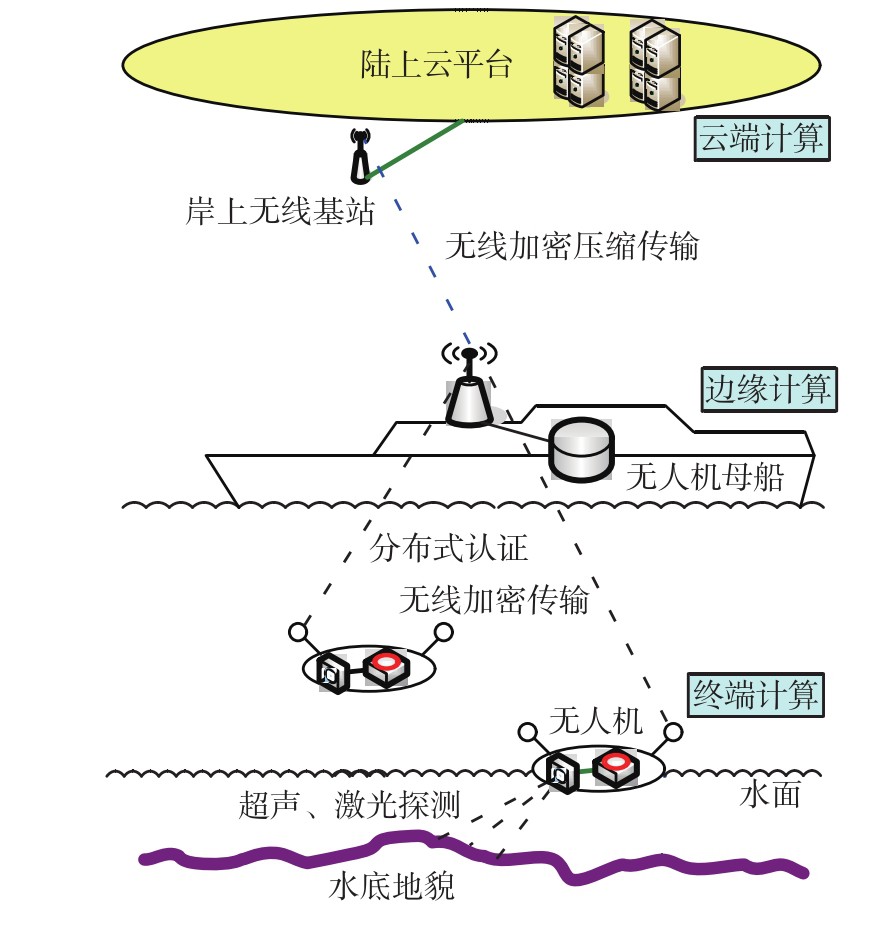
为适应物联网加密传输中大量轻型传感器节点运算性能和能源有限的特点,解决传感器运行RSA(Rivest-Shamir-Adleman)、DHM(Diffie-Hellman-Merkle)、Elgamal等公钥基础设施(PKI)加密算法所面临的运算速度、功耗等瓶颈问题,并简化相应的硬件加密电路逻辑设计,文中提出了一种基于类梅森数的密钥交换快速取模算法(CZ-Mod算法)。CZ-Mod算法利用梅森数的数学特性,使关键的mod(取模)运算的时间复杂度降至O(n)。首先,提出了一种以类梅森数为模数的快速取模运算mod1,使复杂的mod运算变成简单的二进制移位相加运算;其次,提出了一种以任意近似类梅森数的正整数为模数的快速取模运算mod2,在简化mod运算的同时扩大模数的取值范围;然后,对mod1、mod2运算作逻辑电路设计,以简化mod运算的硬件电路;最后,将以上工作应用到物联网节点的密钥交换中,以降低计算的复杂度,提高PKI加密算法的速度。实验测试结果表明:采用CZ-Mod算法的DHM密钥交换速度可达到常规算法的2.5~4倍;CZ-Mod算法精简,适合做物联网传感器的硬件电路设计。
覃健诚, 钟宇, 程喆, 等 . 基于类梅森数的物联网密钥交换快速取模算法[J]. 华南理工大学学报(自然科学版), 2023 , 51(5) : 24 -35 . DOI: 10.12141/j.issn.1000-565X.220355
In order to adapt to the limited computing performance and energy of numerous lightweight sensor nodes in the encrypted transmission of IoT (Internet of Things), this paper proposed a fast modulus algorithm (CZ-Mod algorithm) based on Mersenne-like numbers to slove the bottleneck problems of computing speed, power consumption and so on during the sensors run PKI (Public Key Infrastructure) encryption algorithms such as RSA (Rivest-Shamir-Adleman), DHM (Diffie-Hellman-Merkle), Elgamal, etc., and to simplify the corresponding hardware encrypting circuit logic design. CZ-Mod algorithm uses the mathematic characteristics of Mersenne numbers, and lowers the time complexity of its essential operation mod (modulo) into O(n). Firstly, a fast modulus algorithm mod1 using Mersenne-like numbers as modulus was presented, changing complex mod operation into simple binary shift/add operation; secondly, a fast modulus algorithm mod2 using any positive integers near Mersenne-like numbers as modulus was presented, expanding the modulus value range while simplifying mod operation; and then logic circuits of mod1 and mod2 operations were designed, simplifying mod operation hardware circuit. Finally, the above work was applied to the key exchange of IoT nodes, so as to lower the computing complexity and improve the speed of PKI encryption algorithms. The experiment test results indicate that the speed of DHM key exchange with CZ-Mod algorithm can reach 2.5 to 4 times of that of the conventional algorithm; CZ-Mod algorithm is concise and fits the hardware circuit design for the IoT sensors.
| 1 | HADDADPAJOUH H, DEHGHANTANHA A, PARIZI R M,et al .A survey on internet of things security:requirements,challenges,and solutions [J].Internet of Things,2021,14:100129/1-19. |
| 2 | DIFFIE W, HELLMAN M .New directions in cryptography[J].IEEE Transactions on Information Theory,1976,22(6):644-654. |
| 3 | GAMAL T E .A public key cryptosystem and a signature scheme based on discrete logarithms[J].IEEE Transactions on Information Theory,1985,31:469-472. |
| 4 | RIVEST R L, SHAMIR A, ADLEMAN L .A method for obtaining digital signatures and public-key cryptosystems[J].Communications of the ACM,1978,21(2):120-126. |
| 5 | HU Q L, DUAN M X, YANG Z B,et al .Efficient parallel secure outsourcing of modular exponentiation to cloud for IoT applications[J].IEEE Internet of Things Journal,2020,8(16):12782-12791. |
| 6 | AL-NAJI F H, ZAGROUBA R .A survey on continuous authentication methods in internet-of-things environment[J].Computer Communications,2020,163:109-133. |
| 7 | 张帆 .基于区块链与属性基加密的物联网访问控制研究[D].南京:南京邮电大学,2020. |
| 8 | WU Y, SONG L, LIU L .The new method of sensor data privacy protection for IoT[J].Shock and Vibration,2021:3920579/1-11.DOI:10.1155/2021/3920579 . |
| 9 | 杨宏志,袁凌云,王舒 .基于SM2国密算法优化的区块链设计[J].计算机工程与设计,2021,42(3):622-627. |
| YANG Hong-zhi, YUAN Ling-yun, WANG Shu .Optimized blockchain design based on SM2 algorithm [J].Computer Engineering and Design,2021,42(3):622-627. | |
| 10 | 吴皓威,黄风娇,闫莲,等 .面向可疑中继通信网络的合法窃听方案[J].华南理工大学学报(自然科学版),2022,50(10):70-79. |
| WU Haowei, HUANG Fengjiao, YAN Lian,et al .Legitimate eavesdropping scheme for suspicious relay communication networks[J].Journal of South China University of Technology(Natural Science Edition),2022,50(10):70-79. | |
| 11 | QIN J C, BAI Z Y .Design of new format for mass data compression[J].Journal of China Universes of Posts and Telecommunications,2011,18(1):121-128. |
| 12 | QIN J C, LU Y Q, ZHONG Y .Fast algorithm of truncated Burrows-Wheeler transform coding for data compression of sensors[J].Journal of Sensors,2018:6908760/1-17.DOI:10.1155/2018/6908760 . |
| 13 | QIN J C, LU Y Q, ZHONG Y .Block-split array coding algorithm for long-stream data compression[J].Journal of Sensors,2020:5726527/1-21.DOI:10.1155/2020/5726527 . |
| 14 | QIN J C, LU Y Q, ZHONG Y .Parallel algorithm for wireless data compression and encryption[J].Journal of Sensors,2017:4209397/1-11.DOI:10.1155/2017/4209397 . |
| 15 | 覃健诚,陆以勤 .利用数据压缩编码的混沌同步加密解密方法及其装置:201210386406.9[P].2012-10-13. |
| 16 | LU Y Q, SU W Y, QIN J C .LDPC decoding on GPU for mobile device[J].Mobile Information Systems,2016:7048482/1-6.DOI:10.1155/2016/7048482 . |
| 17 | LU Y Q, WU D W, QIN J C .Wireless authentication center based on embedded Wi-Fi technology[J].WIT Transaction on Information and Communication Technologies,2014,59:387-394. |
| 18 | LU Y Q, ZHAI J, ZHU R H,et al .Study of wireless authentication center with mixed encryption in WSN[J].Journal of Sensors,2016:9297562/1-7.DOI:10.1155/2016/9297562 . |
| 19 | GORDON D M .A survey of fast exponentiation mehods[J].Journal of Algorithms,1998,27(1):129-146. |
| 20 | KNUTH D E .计算机程序设计艺术(卷2)[M].北京:人民邮电出版社,2016. |
| 21 | MOSS A, PAGE D, SMART N .Toward acceleration of RSA using 3D graphics hardware[C]∥ Proceedings of the 11th IMA International Conference on Cryptography and Coding.Cirencester:Springer,2007:364-383. |
| 22 | 乔洋 .基于GPU的RSA算法并行研究与设计及OpenCL实现[D].广州:华南理工大学,2013. |
| 23 | 张盛仕 .基于国密算法加密技术的SoC设计与优化[D].广州:广东工业大学,2019. |
| 24 | 覃健诚,钟宇,陆以勤,等 .基于梅森数的密钥交换或公钥密码加密优化方法及系统:202111668723.5 [P].2022-04-29. |
/
| 〈 |
|
〉 |