

收稿日期: 2022-06-22
网络出版日期: 2022-08-12
基金资助
国家重点研发计划项目(2020YFB1805300)
Security-Aware Scheduling Method for Time-Sensitive Networking
Received date: 2022-06-22
Online published: 2022-08-12
Supported by
the National Key R&D Program of China(2020YFB1805300)
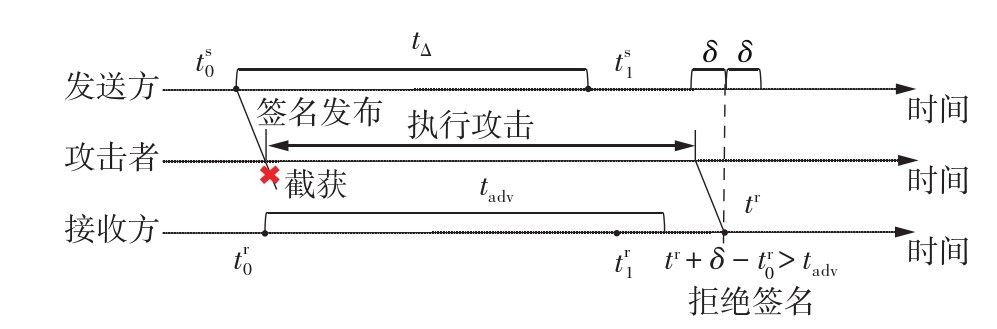
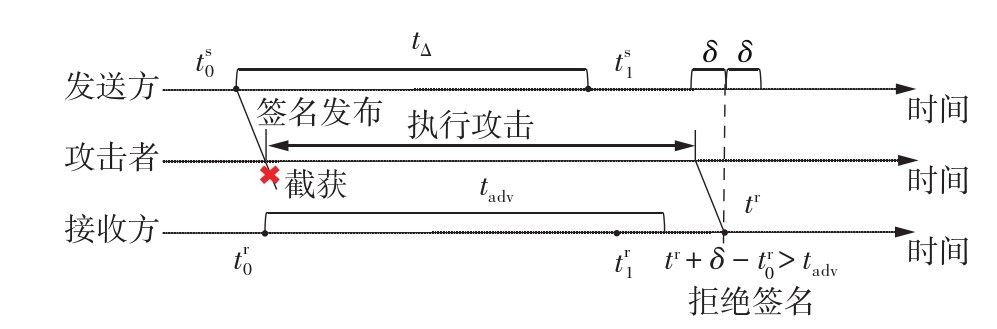
时间敏感网络(TSN)中信息的真实性是系统的关键安全要素,然而直接引入传统安全认证机制会导致系统可调度性和实时性大幅降低。现有的方法仍存在适用场景少、资源消耗高等问题。针对这些问题,文中提出了一种面向TSN的安全感知调度方法。首先基于TSN流量特性设计了一种时间有效的一次性签名安全机制,为消息提供高效的组播源认证;然后提出相应的安全模型对该机制进行评估,描述安全机制对任务和流量的影响;最后对提出的安全感知调度方法进行数学建模,在传统调度约束的基础上,增加了安全机制相关的约束,同时以最小化应用端到端时延为优化目标,使用约束规划进行求解。仿真实验结果表明:改进的一次性签名机制的引入可以有效保护TSN中关键信息的真实性,且对调度的影响有限;在多个基于真实工业场景生成的不同规模测试用例中,产生的应用端到端时延平均仅增加13.3%,带宽消耗平均仅增加5.8%;与其他同类型方法相比,文中方法的带宽消耗更低,更加适用于有严格带宽限制的TSN。
陆以勤 , 谢文静 , 王海瀚 , 陈卓星 , 程喆 , 潘伟锵 , 覃健诚 . 面向时间敏感网络的安全感知调度方法[J]. 华南理工大学学报(自然科学版), 2023 , 51(5) : 1 -12 . DOI: 10.12141/j.issn.1000-565X.220394
The authenticity of information is the key security factor of system in time-sensitive networking (TSN). However, the direct introduction of traditional security authentication mechanism will lead to a significant reduction in schedulability of the system. The existing methods still have the problems of few application scenarios and high resource consumption. To address this problem, a security-aware scheduling method for TSN was proposed. Firstly, based on the traffic characteristics of TSN, a time-efficient one-time signature security mechanism was designed to provide efficient multicast source authentication for messages. Secondly, the corresponding security model was proposed to evaluate the mechanism and describe the impact of the security mechanism on tasks and traffic. Finally, the proposed security-aware scheduling method was modeled mathematically. On the basis of traditional scheduling constraints, some constraints related to security mechanisms were added. At the same time, the optimization objective was to minimize the end-to-end delay of applications, and constraint programming was used to solve the problem. Simulation results show that the introduction of the improved one-time signature mechanism can effectively protect the authenticity of key information in TSN, and has limited impact on scheduling. In multiple test cases of different sizes generated based on real industrial scenarios, the average end-to-end delay and bandwidth consumption of the generated applications only increased by 13.3% and 5.8% respectively. Compared with other similar methods, this method consumes less bandwidth, thus more suitable for TSN networks with strict bandwidth restrictions.
Key words: time-sensitive networking; security; scheduling; constraint programming
| 1 | BELLO L L, STEINER W .A perspective on IEEE time-sensitive networking for industrial communication and automation systems[J].Proceedings of the IEEE,2019,107(6):1094-1120. |
| 2 | ASHJAEI M, BELLO L L, DANESHTALAB M,et al .Time-sensitive networking in automotive embedded systems:state of the art and research opportunities[J].Journal of Systems Architecture,2021,117:102137/1-15. |
| 3 | CRACIUNAS S S, OLIVER R S, CHMELíK M,et al .Scheduling real-time communication in IEEE 802.1 Qbv time sensitive networks[C]∥ Proceedings of the 24th International Conference on Real-Time Networks and Systems.Brest:ACM,2016:183-192. |
| 4 | DüRR F, NAYAK N G .No-wait packet scheduling for IEEE time-sensitive networks (TSN)[C]∥ Proceedings of the 24th International Conference on Real-Time Networks and Systems.Brest:ACM,2016:203-212. |
| 5 | RAAGAARD M L,POP P .Optimization algorithms for the scheduling of IEEE 802.1 time-sensitive networking (TSN) [R/OL].(2017-01-15)[2022-05-06].. |
| 6 | 张彤,冯佳琦,马延滢,等 .时间敏感网络流量调度综述[J].计算机研究与发展,2022,59(4):747-764. |
| ZHANG Tong, FENG Jiaqi, MA Yanying,et al .Survey on traffic scheduling in time-sensitive networking [J].Journal of Computer Research and Development,2022,59(4):747-764. | |
| 7 | ZHANG L, GOSWAMI D, SCHNEIDER R,et al .Task-and network-level schedule co-synthesis of Ethernet-based time-triggered systems[C]∥ Proceedings of the 19th Asia and South Pacific Design Automation Conference.Singapore:IEEE,2014:119-124. |
| 8 | CRACIUNAS S S, OLIVER R S .Combined task-and network-level scheduling for distributed time-riggered systems[J].Real-Time Systems,2016,52(2):161-200. |
| 9 | MAHFOUZI R, AMINIFAR A, SAMII S,et al .Security-aware routing and scheduling for control applications on Ethernet TSN networks[J].ACM Transactions on Design Automation of Electronic Systems,2019,25(1):1-26. |
| 10 | ZHAO R, QIN G,LYU Y,et al .Security-aware scheduling for TTEthernet-based real-time automotive systems[J].IEEE Access,2019,7:85971-85984. |
| 11 | PERRIG A, CANETTI R, SONG D,et al .Efficient and secure source authentication for multicast[C]∥ Proceedings of 2001 Network and Distributed System Security Symposium.San Diego:Internet Society,2001:35-46. |
| 12 | REUSCH N,POP P, CRACIUNAS S S .Work-in-progress:safe and secure configuration synthesis for TSN using constraint programming[C]∥ Proceedings of 2020 IEEE Real-Time Systems Symposium.Houston:IEEE,2020:387-390. |
| 13 | WANG Q, KHURANA H, HUANG Y,et al .Time valid one-time signature for time-critical multicast data authentication[C]∥ Proceedings of IEEE INFOCOM 2009.Rio de Janeiro:IEEE,2009:1233-1241. |
| 14 | REYZIN L, REYZIN N .Better than BiBa:short one-time signatures with fast signing and verifying[C]∥ Proceedings of the 7th Australasian Conference on Information Security and Privacy.Melboume:Springer,2002:144-153. |
| 15 | Google .CP-SAT solver [DB/OL]. (2022-03-05)[2022-05-06].. |
/
| 〈 |
|
〉 |